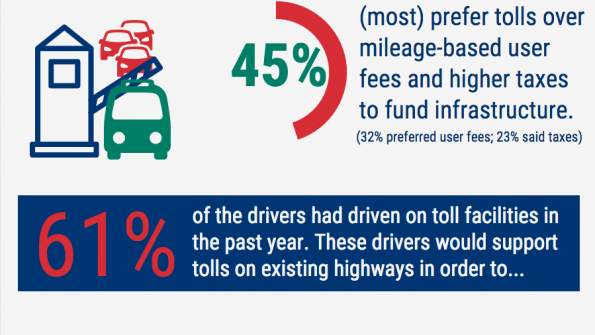
Infographic: What drivers think about tolls
Americans support tolls when they're used to directly fund infrastructure projects and when they help drivers avoid traffic and save time. Learn more about public perception on tolling by viewing this infographic.
Most Recent
-

2023 Crown Communities Award winner: Ringling Trail Complete Streets project
In 2024, pedestrians, cyclists, scooter operators and public transit users can rely on the Ringling Trail Complete Streets initiative for safe access. The project has helped boost economic activity for surrounding areas and businesses, while elevating the overall quality of life for residents. For all of these reasons, this Sarasota, Fla. project has been selected […]
-

Cities-counties need to monitor fleet maintenance and carefully spend tax dollars
The public sector faces high debt levels, stressed budgets and wide-ranging priorities, says Brian Fairweather, vice president of public sector at Uptake, a developer of fleet maintenance software used by all levels of government to help reduce maintenance costs, maximize asset lifespan and improve operational systems. Fairweather says government officials have been getting the following […]
-

Why working with the wrong tax escrow payment processor can wreak havoc on government operations
Mortgage tax escrow payments for both local property owners and businesses continue to serve as a crucial source of revenue for local governments. Among these payments, timely settlement of local property taxes holds particular significance. It’s not just about fulfilling a financial obligation; rather, it plays a pivotal role in maintaining stability, both for individual […]
-

For the public sector, security and compliance are just good business
State and local officials in charge of distributing public funds understand that security and compliance must be a top priority, but it can feel like a challenge to be fully prepared for audits. First, government organizations face a significant challenge in securing cyber infrastructure and protecting the personal data of their constituents from malicious actors. […]